Commvault Unveils Clumio Backtrack - Near Instant Dataset Recovery in S3
Is the Mandela Effect Leaving Your AWS Data Vulnerable?
Humanity’s collective memory can be a little fuzzy. Case-in-point: The Mandela Effect, or the phenomenon of large groups of people misremembering the same fact or event in a similar way. The effect is named after Nelson Mandela, who many people believe died in prison in the 1980s despite the fact that he actually went on to become President of South Africa in the 1990s.
A Few Examples of the Mandela Effect:
- Although most people remember childhood character Curious George as being drawn with a tail, he does not have one.
- Many people believe there is a brand of peanut butter called “Jiffy” but there is not. There’s Jif, and there’s Skippy, but no Jiffy.
- In the iconic scene in “Silence of the Lambs,” Hannibal Lecter does not say “Hello Clarice” as many people remember. He says “good morning.”
The Mandela Effect in the Cloud
The Mandela effect is not just a pop culture phenomenon, it exists in the world of enterprise technology, too. It’s a common misconception that data stored in the cloud is automatically backed up. The truth is that cloud providers operate on a shared responsibility model, in which the cloud provider is responsible for the security of the software, hardware and infrastructure, but not customers’ data.
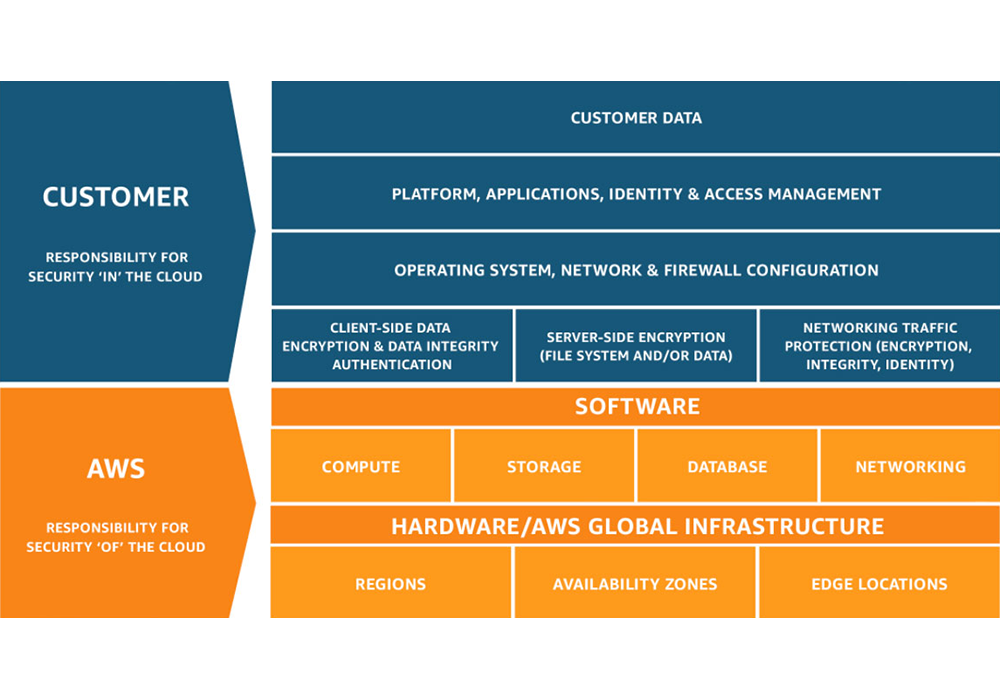 Shared Responsibility Model from AWS
Shared Responsibility Model from AWS
For example, when AWS refers to their highly durable Amazon S3 service, it’s true that the platform is incredibly durable, which means you’re unlikely to experience any trouble with their systems or infrastructure. However, this has nothing to do with protecting your data from accidental deletions, ransomware attacks or insider threats. According to the shared responsibility model, that’s your job.
Taking Steps to Protect Your Cloud Data
Understanding your part of the shared responsibility model is your first step. Figuring out how to protect your data is the next. Here are a few resources for your consideration:
- Step through an explanation of the different uses of replication, snapshots and backup in data protection in Clumio Systems Engineer Nic Hernandez’s blog.
- Many Clumio customers have first tried to build their own data protection solutions, before deciding that it wasn’t the best use of their resources given that a simple, cost-effective solution is available to them. Charles Goforth considers the DIY angle in his blog.
- Another misconception is that a third party data protection solution adds cost to the business. But that doesn’t take into consideration savings realized with management cost reduction. ESG conducted an Economic Value Validation Report to help organizations evaluate the potential savings with Clumio. Spoiler: enterprises have saved millions with Clumio over other backup solutions.
Customers love working with Clumio because they get air-gapped, immutable data protection with incredibly fast time to value while SaaS simplicity ensures fast and simple ingest, cataloging, search and recovery at any scale. Clumio allows customers to automate protection of their AWS and Microsoft 365 data, saving time and resources that allow them to focus on strategic initiatives and reducing TCO compared with other options.
Don’t let data protection misconceptions leave you vulnerable. Say goodbye to The Mandela Effect and get The Clumio Effect.